Carry-based Differential Power Analysis (CDPA)

We present Carry-based Differential Power Analysis (CDPA) — a new side-channel attack targeting algorithms that use arithmetic addition. Applied to HMAC-SHA-2, CDPA enables full key recovery from power traces, both in simulation and on FPGA hardware. With as few as 30K traces, secret keys can be recovered in some cases, allowing for forging the HMAC-SHA-2 signature of any message, and with 275K traces, the success rate reaches 100%. This demonstrates that even pure hardware implementations of HMAC-SHA-2 are vulnerable unless properly protected. To our knowledge, this is the first successful non-profiling attack on hardware HMAC-SHA-2.
Redundancy AES Masking Basis for Attack Mitigation

Here we present RAMBAM, our patented novel concept of designing countermeasures against side-channel attacks and SIFA on AES using redundant representations of finite field elements. It enables trade-offs between gate count, maximal frequency, performance, level of robustness to first and higher-order side-channel attacks and SIFA-1. We present an analytical model that explains the leakage reduction, and a leakage assessment using TVLA methodology on an FPGA board, showing resilience to at least 348M traces with 16 Sboxes.
SEMISRAEL Tech Webinar: Semiconductor Security Simplified
Attackers can now breach your device for just a few hundred dollars unless robust security measures are in place. Watch our webinar to learn how our solution ensures you no longer have to compromise between security and functionality.
WHAT ARE THE DATA REQUIREMENTS FOR SIDECHANNEL STUDIO?
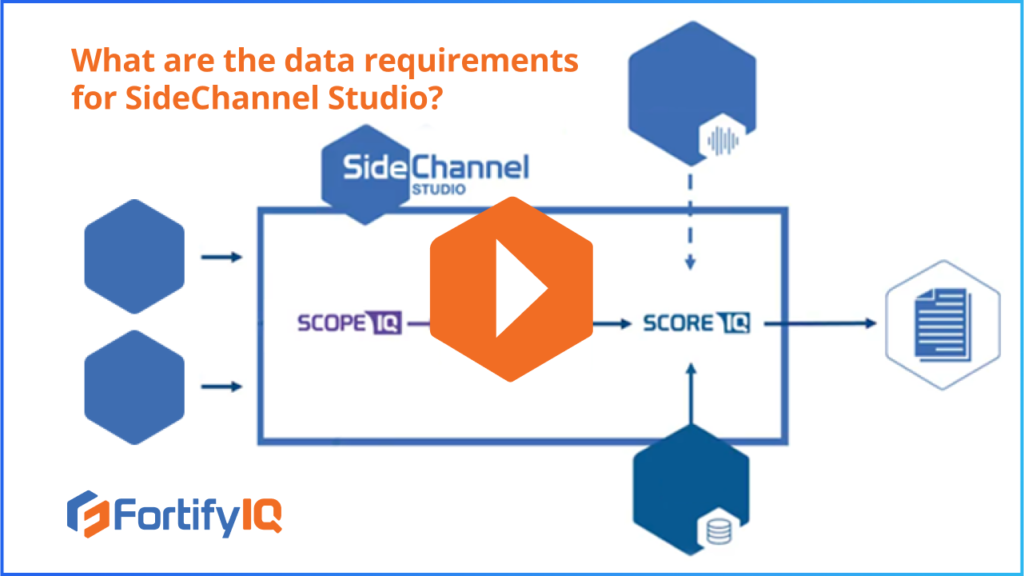
WHAT ARE THE DATA REQUIREMENTS FOR SIDECHANNEL STUDIO? The ScopeIQ simulator of SideChannel studio receives 3 major inputs: the gate level netlist, the target cell library, and a test bench. Side-channel traces produced by ScopeIQrunning are fed to the side-channel trace analyzer called ScoreIQ. Customers can then choose which plugin attack module ScoreIQshould run. Depending […]