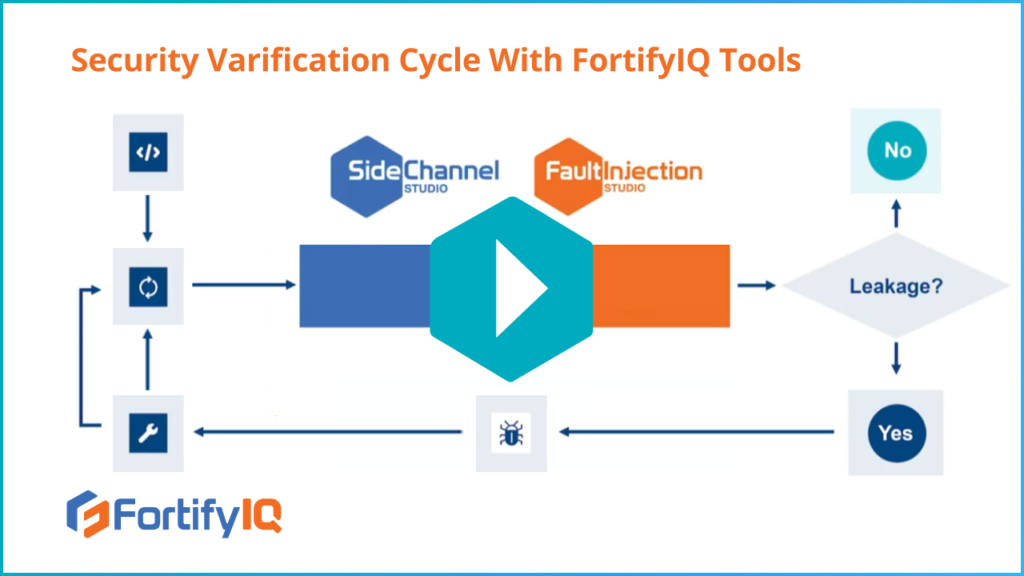
Without FortifyIQ’s tools, today’s state of the verification process is costly, tedious, and can take several months. How can you perform security verification in a reasonable amount of time and for a reasonable cost? This is precisely what FortifyIQ makes possible by closing the gap, allowing you to verify the security in the pre-silicon stage—in the same way the functionality is verified. In other words, FortifyIQ revolutionizes the process, accelerating your entire cycle. This video shows how the virtual capabilities offered will run your security verification while you circumvent physical verification labs.