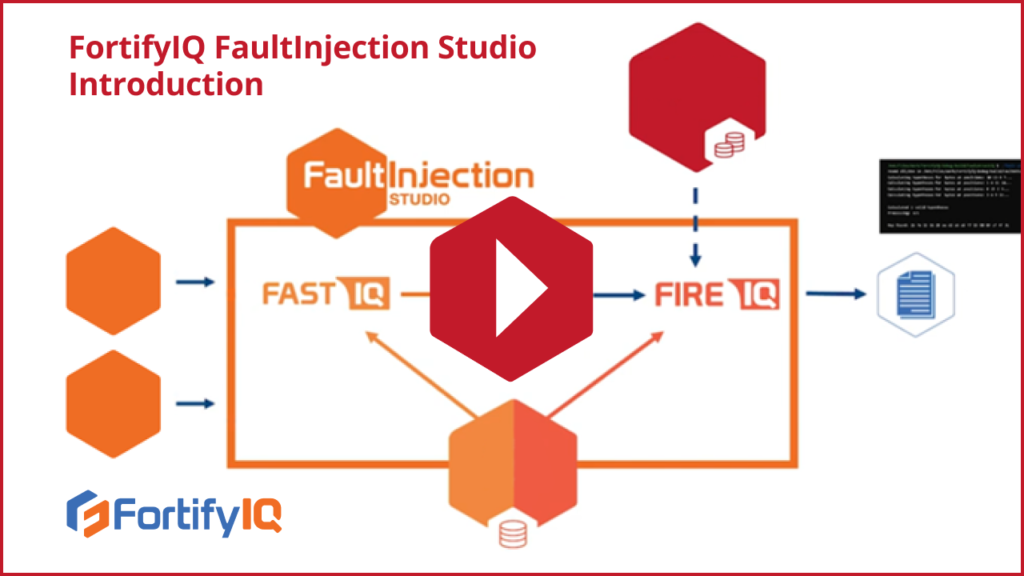
In this video, you will get a brief introduction to the components and operation of FaultInjection studio. Fault Attack Simulator and Test (FastIQ), as the name suggests, simulates fault attacks. First, FastIQ receives its inputs—the gate level netlist, the target cell library, and the simple test bench—and simulates a specific fault injection attack using an attack-specific plugin. Its output is a list of attained results, either correct or corrupted, along with the corresponding faults. These results are then passed to the FireIQ analyzer, which in turn produces output reports. If it produces a key, it proves that the hardware protection was insufficient. Watch the video to learn more!