WHAT ARE THE DATA REQUIREMENTS FOR FAULTINJECTION STUDIO?
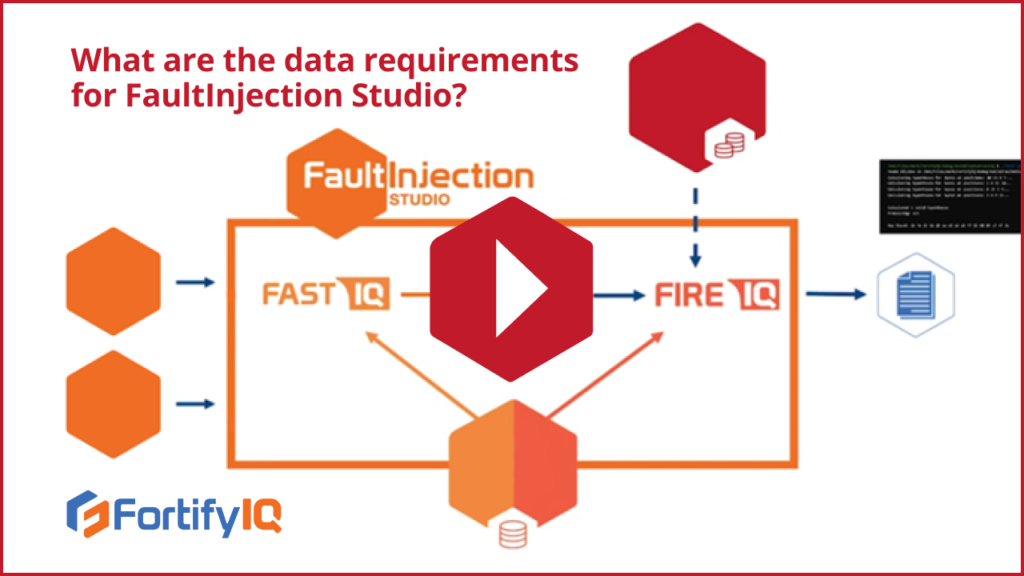
Video Technical Details WHAT ARE THE DATA REQUIREMENTS FOR FAULTINJECTION STUDIO? Active FortifyIQ customers receive updates to the library of attack plugins, and they also have the ability to add their own pairs of attack plugins written in C++ or Python. If they want to use FaultInjection Studio for a specific attack, all they need […]
WHAT ARE THE DATA REQUIREMENTS FOR SIDECHANNEL STUDIO?
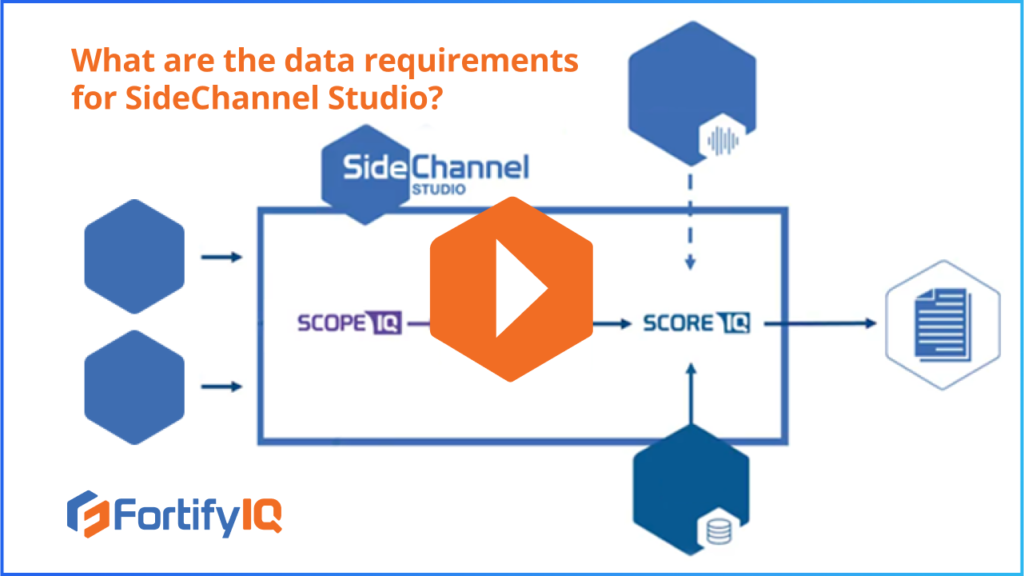
Video Technical Details WHAT ARE THE DATA REQUIREMENTS FOR SIDECHANNEL STUDIO? The ScopeIQ simulator of SideChannel studio receives 3 major inputs: the gate level netlist, the target cell library, and a test bench. Side-channel traces produced by ScopeIQrunning are fed to the side-channel trace analyzer called ScoreIQ. Customers can then choose which plugin attack module […]
WHAT IS TEST VECTOR LEAKAGE ASSESSMENT?

Video Technical Details WHAT IS TEST VECTOR LEAKAGE ASSESSMENT? You want to know at the pre-silicon stage whether your device is going to pass the TVLA test or not. This is especially critical if you are going for NIST certification. Check out this video to explore the test methodology adopted by NIST as part of […]
What products and services does FortifyIQ offer?

Video Technical Details WHAT PRODUCTS AND SERVICES DOES FortifyIQ OFFER IN THE FIELD OF PRE-SILICON VALIDATION? FortifyIQ’s goal is to provide maximum security against side-channel and fault injection attacks across the entire computing spectrum, including at the pre-silicon stage. To that end, they have established two studios for pre-silicon verification – SideChannel Studio and FaultInjection […]
DOES FORTIFYIQ SUPPORT SECURITY VERIFICATION STANDARDS?

Video Technical Details DOES FORTIFYIQ SUPPORT SECURITY VERIFICATION STANDARDS? NIST certification—required for projects related to the U.S. government, and required by some private organizations—verifies when there is no side-channel leakage in your devices. TVLA (Test Vector Leakage Assessment) testing also gauges the number of side channel leakages. These two certifications are typically run in tandem […]