Carry-Based Differential Power Analysis and its Application to Attacking HMAC SHA-2

We present Carry-based Differential Power Analysis (CDPA) — a new side-channel attack targeting algorithms that use arithmetic addition. Applied to HMAC-SHA-2, CDPA enables full key recovery from power traces, both in simulation and on FPGA hardware. With as few as 30K traces, secret keys can be recovered in some cases, allowing for forging the HMAC-SHA-2 signature of any message, and with 275K traces, the success rate reaches 100%. This demonstrates that even pure hardware implementations of HMAC-SHA-2 are vulnerable unless properly protected. To our knowledge, this is the first successful non-profiling attack on hardware HMAC-SHA-2.
Redundancy AES Masking Basis for Attack Mitigation

Here we present RAMBAM, our patented novel concept of designing countermeasures against side-channel attacks and SIFA on AES using redundant representations of finite field elements. It enables trade-offs between gate count, maximal frequency, performance, level of robustness to first and higher-order side-channel attacks and SIFA-1. We present an analytical model that explains the leakage reduction, and a leakage assessment using TVLA methodology on an FPGA board, showing resilience to at least 348M traces with 16 Sboxes.
SEMISRAEL Tech Webinar

Attackers can now breach your device for just a few hundred dollars unless robust security measures are in place. Watch our webinar to learn how our solution ensures you no longer have to compromise between security and functionality.
FortifyIQ SideChannel Studio Analysis Results
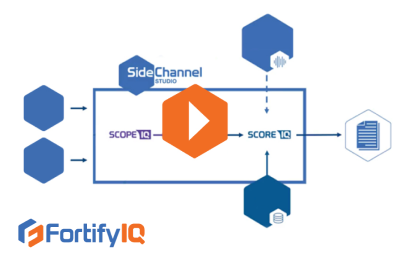
Learn how SideChannel Studio helps you find the source of side-channel leakage through a series of explanatory screenshots. Watch this detailed video now!
FORTIFYIQ PRODUCTS AND TECHNOLOGY OVERVIEW

Video Overviews FORTIFYIQ PRODUCTS AND TECHNOLOGY OVERVIEW Unlike software security, hardware security cannot be added to an existing chip. Therefore, it is essential to plan and implement defenses against side-channel and fault injection attacks before a chip is manufactured. You need the help of a highly qualified specialist to design defenses against such attacks. The […]
FortifyIQ protected IP introduction

Get a deep dive into the world of FortifyIQ’s protected IP cores and ultra-high bandwidth engines based on these IP cores. Learn all about the different core configurations and much more in this introductory video.
FORTIFYIQ FAULTINJECTION STUDIO INTRODUCTION
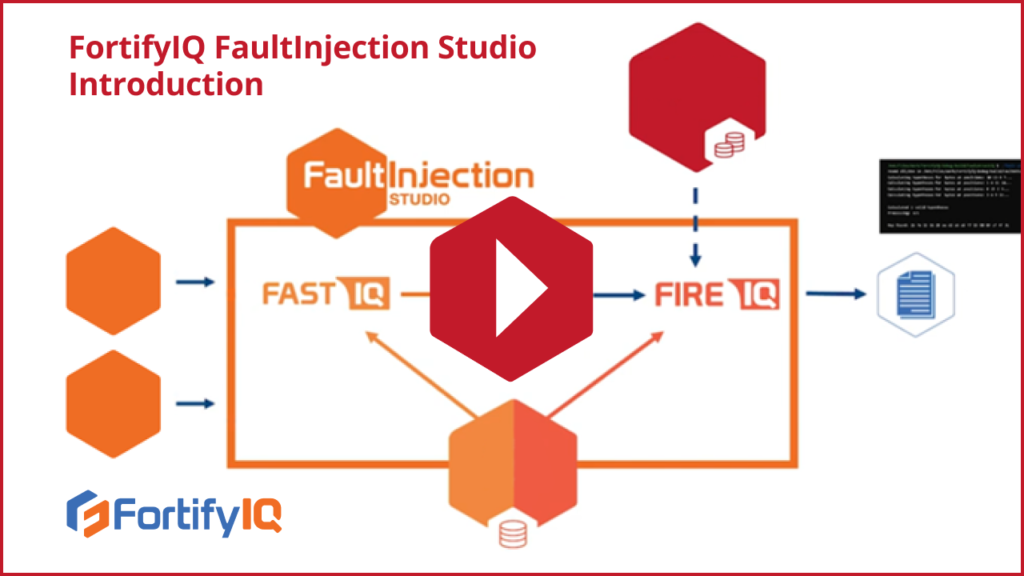
Video Overviews FORTIFYIQ FAULTINJECTION STUDIO INTRODUCTION In this video, you will get a brief introduction to the components and operation of FaultInjection studio. Fault Attack Simulator and Test (FastIQ), as the name suggests, simulates fault attacks. First, FastIQ receives its inputs—the gate level netlist, the target cell library, and the simple test bench—and simulates a […]
HARDWARE SECURITY ATTACKS – A CLEAR AND PRESENT DANGER

Video Overviews HARDWARE SECURITY ATTACKS – A CLEAR AND PRESENT DANGER There is a lot of secret data around us. The most valuable secrets such as cryptographic keys should be given the best possible protections. The key to doing that is burying the data in hardware. Though nowadays, you need more than just that to […]
HOW DO YOU VERIFY THAT YOUR DESIGN IS PROTECTED AGAINST SIDE-CHANNEL AND FAULT INJECTION ATTACKS?
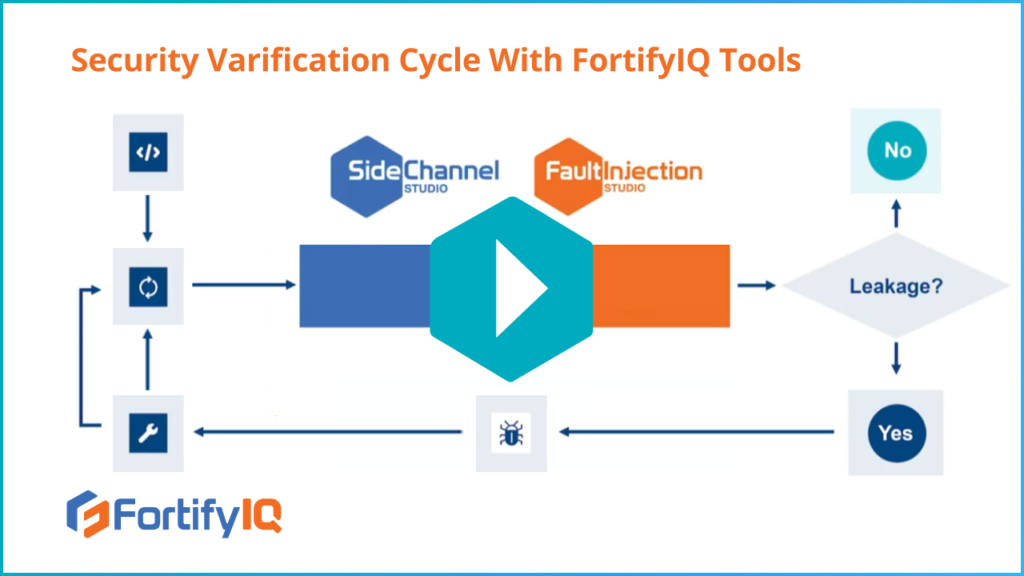
Video Technical Details HOW DO YOU VERIFY THAT YOUR DESIGN IS PROTECTED AGAINST SIDE-CHANNEL AND FAULT INJECTION ATTACKS? Without FortifyIQ’s tools, today’s state of the verification process is costly, tedious, and can take several months. How can you perform security verification in a reasonable amount of time and for a reasonable cost? This is precisely […]
HOW FAST IS THE FORTIFYIQ HARDWARE VERIFICATION SOLUTION?
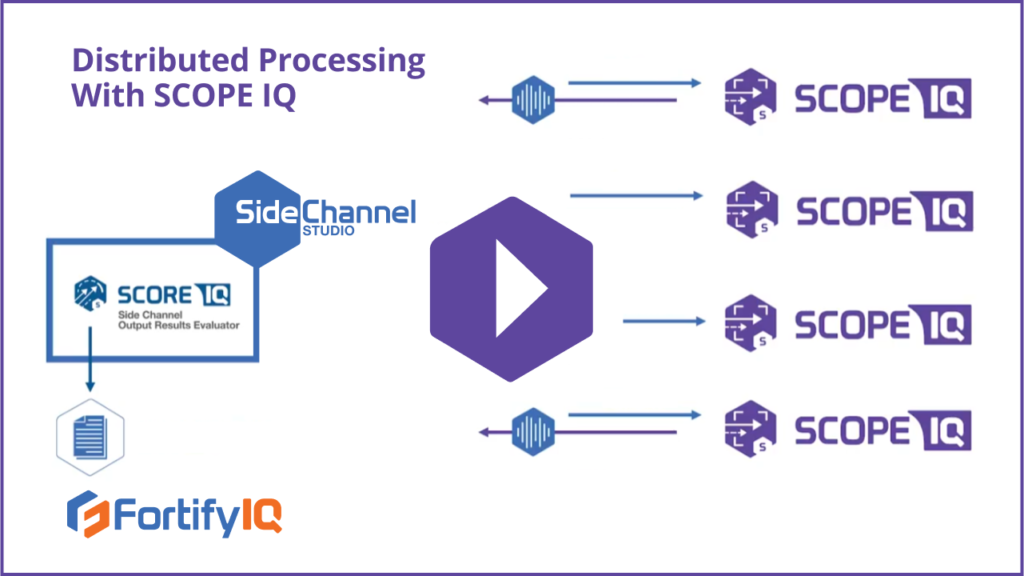
Video Technical Details HOW FAST IS THE FORTIFYIQ HARDWARE VERIFICATION SOLUTION? How fast can you create traces using ScopeIQ? Watch this video and learn how to focus on specific portions of your design and target the simulation on the security algorithm—to increase productivity and dramatically improve the simulation turnaround time. You’ll also learn about how […]