FORTIFYIQ PRODUCTS AND TECHNOLOGY OVERVIEW

FORTIFYIQ PRODUCTS AND TECHNOLOGY OVERVIEW Unlike software security, hardware security cannot be added to an existing chip. Therefore, it is essential to plan and implement defenses against side-channel and fault injection attacks before a chip is manufactured. You need the help of a highly qualified specialist to design defenses against such attacks. The question is […]
HARDWARE SECURITY ATTACKS – A CLEAR AND PRESENT DANGER

HARDWARE SECURITY ATTACKS – A CLEAR AND PRESENT DANGER There is a lot of secret data around us. The most valuable secrets such as cryptographic keys should be given the best possible protections. The key to doing that is burying the data in hardware. Though nowadays, you need more than just that to secure your […]
HOW DO YOU VERIFY THAT YOUR DESIGN IS PROTECTED AGAINST SIDE-CHANNEL AND FAULT INJECTION ATTACKS?
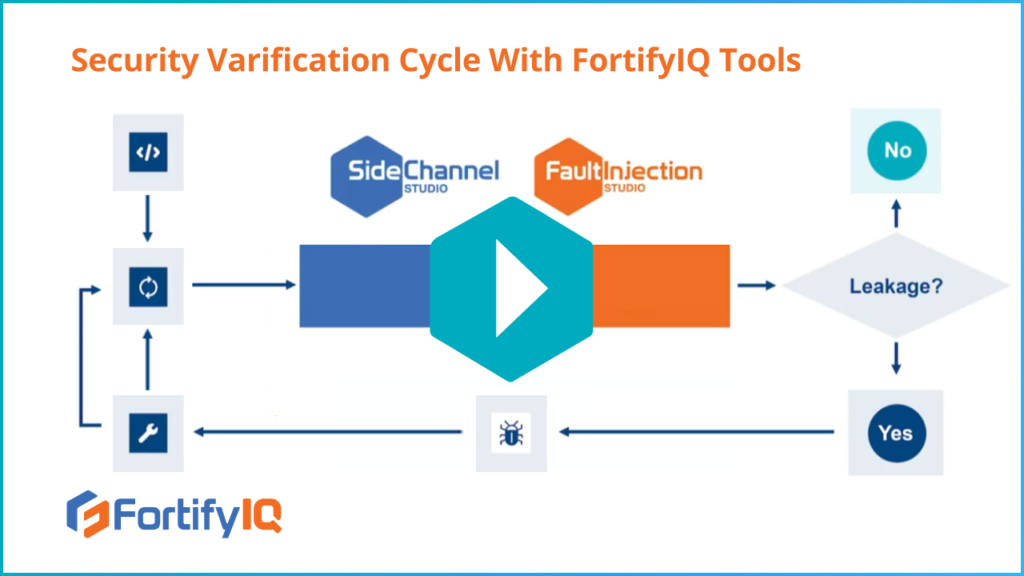
HOW DO YOU VERIFY THAT YOUR DESIGN IS PROTECTED AGAINST SIDE-CHANNEL AND FAULT INJECTION ATTACKS? Without FortifyIQ’s tools, today’s state of the verification process is costly, tedious, and can take several months. How can you perform security verification in a reasonable amount of time and for a reasonable cost? This is precisely what FortifyIQ makes […]
HOW FAST IS THE FORTIFYIQ HARDWARE VERIFICATION SOLUTION?
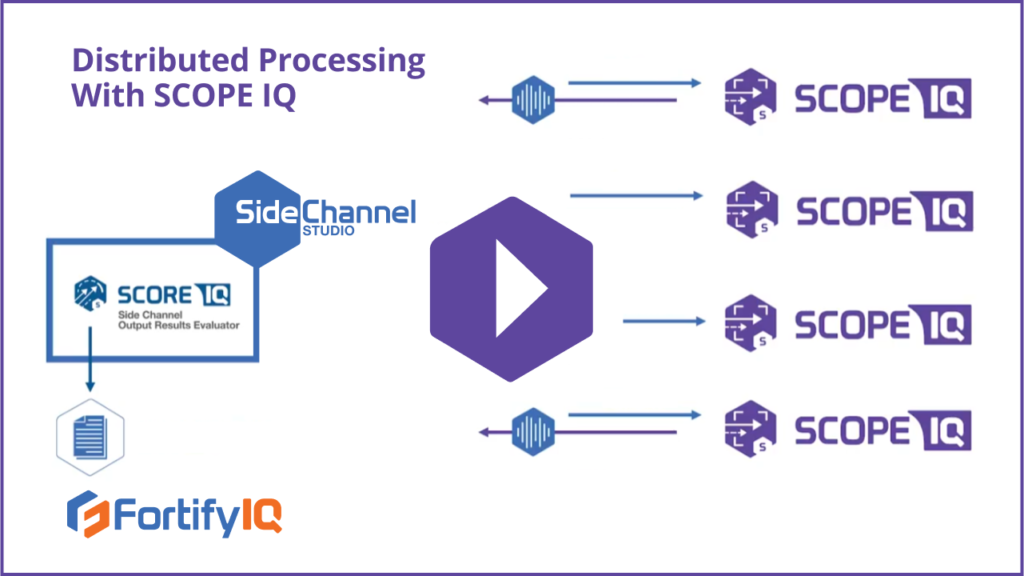
HOW FAST IS THE FORTIFYIQ HARDWARE VERIFICATION SOLUTION? How fast can you create traces using ScopeIQ? Watch this video and learn how to focus on specific portions of your design and target the simulation on the security algorithm—to increase productivity and dramatically improve the simulation turnaround time. You’ll also learn about how SideChannel Studio can […]
WHAT ARE THE DATA REQUIREMENTS FOR FAULTINJECTION STUDIO?
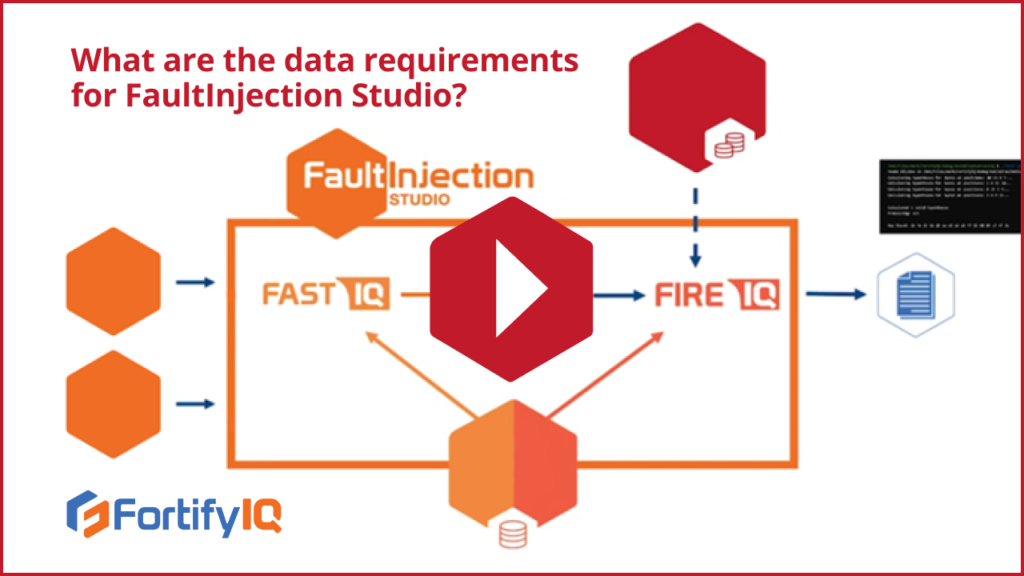
WHAT ARE THE DATA REQUIREMENTS FOR FAULTINJECTION STUDIO? Active FortifyIQ customers receive updates to the library of attack plugins, and they also have the ability to add their own pairs of attack plugins written in C++ or Python. If they want to use FaultInjection Studio for a specific attack, all they need to really do […]
WHAT ARE THE DATA REQUIREMENTS FOR SIDECHANNEL STUDIO?
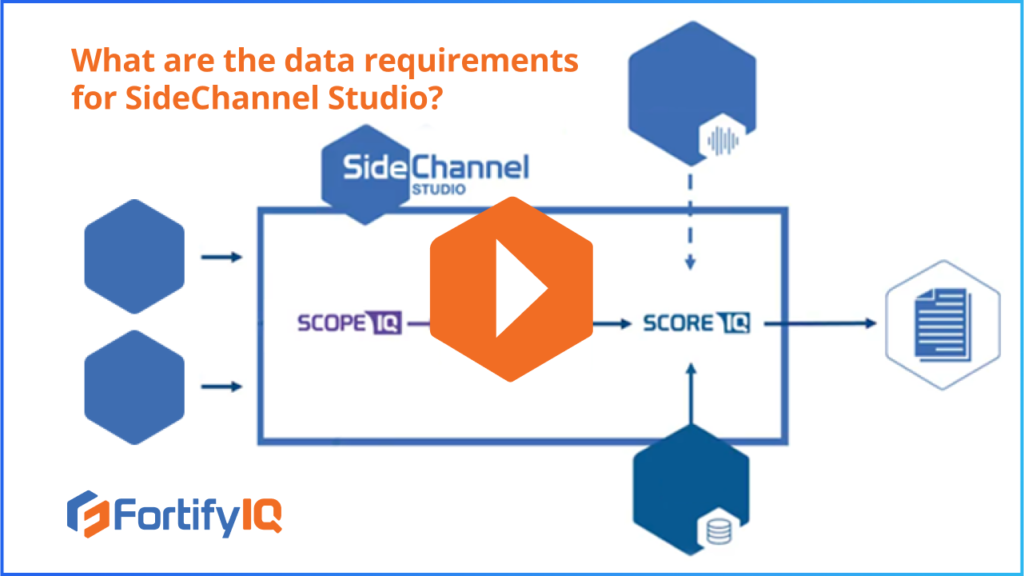
WHAT ARE THE DATA REQUIREMENTS FOR SIDECHANNEL STUDIO? The ScopeIQ simulator of SideChannel studio receives 3 major inputs: the gate level netlist, the target cell library, and a test bench. Side-channel traces produced by ScopeIQrunning are fed to the side-channel trace analyzer called ScoreIQ. Customers can then choose which plugin attack module ScoreIQshould run. Depending […]