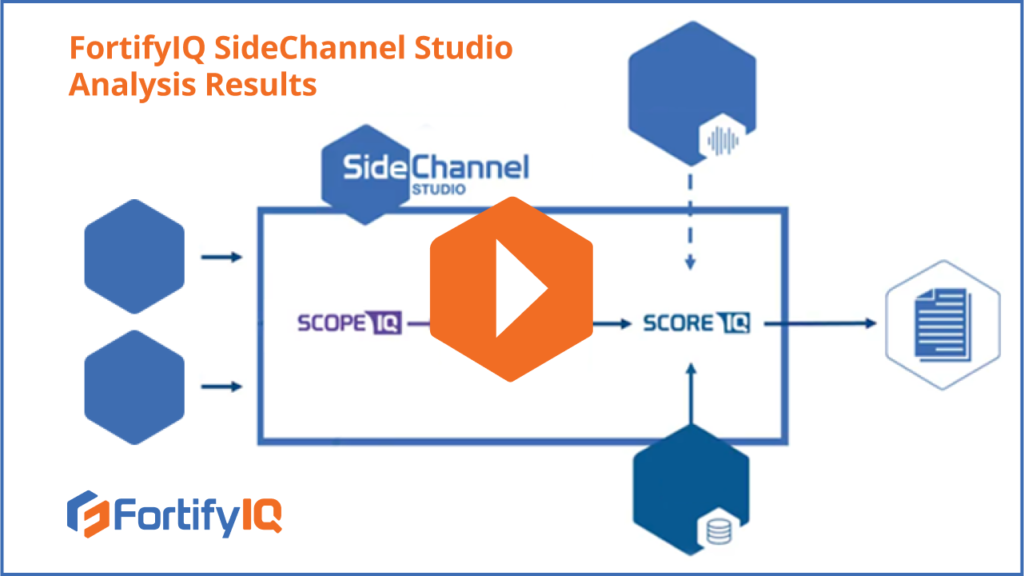
ScopeIQ is a special purpose side-channel simulator that produces traces. These traces are fed into ScoreIQ, the side-channel trace analyzer. ScoreIQ then performs one of the attacks from the library or the TVLA assessment of side-channel leakage. The results are presented in graphical and digital forms.
In this video, you will get to check out screenshots of ScoreIQ successfully running an attack on an unprotected AES implementation and presenting the revealed value of the secret key. You will also get to explore a use case that illustrates how SideChannel Studio helps you find sources of leakage, and much more.